Services
Every Sanctum service has an enabled flag in instance.yaml. Disabled services are skipped by the plist generator, excluded from the dashboard, and ignored by the watchdog. This page is the authoritative catalog of all services in the platform.
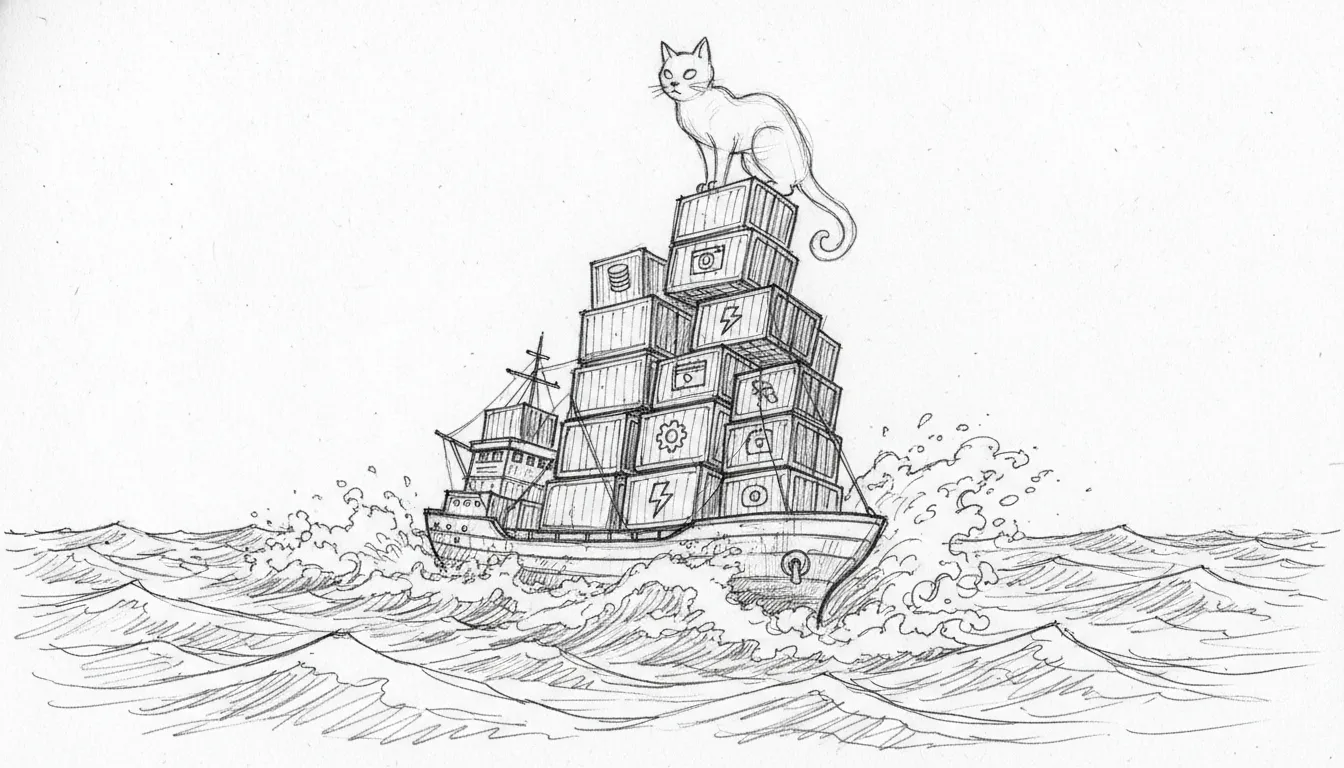
There are a lot of them. What started as “I’ll just automate the speakers” has become something that requires its own port allocation strategy and a documentation site. This is either a haus automation system or a small government. The line blurred around service number twelve and never came back. Thirty-eight services now — enough to staff two Habs benches on a good night, and they all think they’re the centreman. Each with a launchd unit, a port, a plist, and opinions about what should have been done on Tuesday.
Core Services
Section titled “Core Services”A $600 aluminum rectangle shouldering the responsibilities of a small government. These six services are the load-bearing walls. Remove any one and the haus doesn’t just creak — it files a complaint with the watchdog, the dashboard goes red, and your family asks why the chat isn’t working during dinner.
Every hub node runs all of them. No exceptions, no “I’ll enable that later.” Later is where haus automation projects go to die.
| Service | Port | LaunchAgent / Unit | Description |
|---|---|---|---|
| DenchClaw Gateway | 1977 | com.sanctum.gateway | Mac-side agent gateway. Runs Jocasta (the Archivist — CRM data and communications) and exposes the agent API. |
| Home Assistant | 8123 | Docker container | Home automation hub. Bridge-networked Docker container with HomeKit bridge on port 21063. |
| Command Center | 1111 | com.sanctum.dashboard | Web dashboard for service status, agent activity, and system health. |
| Health Center | 2222 | com.sanctum.health-center | Digital twin portal — health, wellness, and haushold telemetry. Twin twos for the twin. |
| Holocron (Dench) | 1977 | com.sanctum.dench | Family chat interface. Bound to LAN, token-authenticated. Accessible at http://holocron/. |
| Dench Proxy | 80 | com.sanctum.dench-proxy | LaunchDaemon (runs as root). Reverse proxy from port 80 to Holocron on port 1977. |
Config Example
Section titled “Config Example”services: openclaw_gateway: enabled: true port: 1977 home_assistant: enabled: true port: 8123 homekit_port: 21063 dashboard: enabled: true port: 1111AI Services
Section titled “AI Services”Five AI models sharing a single Mac Mini is either an act of architectural genius or the opening scene of a disaster movie. We’ve been running it for months. The jury remains out, but the Mac Mini hasn’t caught fire, so we’re calling it genius until the thermal paste says otherwise.
This is where Apple Silicon earns its keep. The M4 Pro runs local inference, text-to-speech, and a voice agent simultaneously — the kind of multitasking that would make an Intel chip file a workers’ comp claim.
| Service | Port | Codename | LaunchAgent | Description |
|---|---|---|---|---|
| LM Studio | 1234 | — | com.sanctum.lmstudio-bridge | Local LLM inference for VM agents. Currently serving qwen2.5-coder-14b-instruct via socat bridge from 10.10.10.1:1234 to 127.0.0.1:1234. API key: lm-studio. |
| Council MLX | 1337 | leet — the local workhorse | com.sanctum.mlx | Pure-Rust sanctum-mlx server. Serves Qwen3.6-35B-A3B-4bit with TurboQuant Slice 4a fused Metal kernel. mTLS-only. The 27B-distilled era ended 2026-04-22 when the council moved to the 35B MoE. |
| TTS Voice | 8008 | BOOB — Yoda’s mouth | com.sanctum.yoda-tts-worker | Qwen3-TTS via mlx-audio (workers.tts_server). XTTS retired 2026-04-19 once Qwen3-TTS proved equal quality with lower memory pressure. |
| Voice Agent | 1138 | — | com.sanctum.voice-agent | Yoda voice interface. Integrates with Sonos speakers via the Sonos Bridge REST API on port 1969. |
| Sanctum Proxy | 4040 | .40 caliber — the gateway | com.sanctum.server | LLM routing proxy on port 4040 (binary: proxyd). Single Rust binary handling tiered model routing, prompt caching, request sanitization, PII scrubbing, and automatic fallback. KeepAlive enabled. |
| Memory Vault | 42069 | Nice. | com.sanctum.memory-vault | Long-term memory store for agent context. SQLite vault at ~/.sanctum/memory/.vault.db, consolidates every 6h. SSE transport for MCP clients. |
| Jina Reranker | 42070 | The Pair Port | com.sanctum.reranker | Jina v2 reranking server. Companion to Memory Vault on 42069 — the two travel together by design. Improves RAG precision for long-context memory queries. |
Model Routing — 3-Tier Architecture
Section titled “Model Routing — 3-Tier Architecture”Agents use a 3-tier model strategy ranked by the Carmack Olympics benchmark system. The Smart Router dispatches each request based on model field, glob patterns, or intent keywords. When the primary tier is unavailable, traffic cascades down through the chain until it hits local Metal inference. The generator always kicks in.
| Tier | Model | Port | Agents | Fallback |
|---|---|---|---|---|
cloud | Claude Opus 4.7 (Anthropic) | :4040 proxy | Windu, Mothma, Jocasta | Coder-14B → Council MLX → error |
council-ops | Qwen 2.5 Coder 14B (LM Studio) | :1234 | Yoda, QuiGon, Ahsoka | Council MLX → error |
council-secure | Gemma4+LoRA (sanctum-mlx) | :1337 | Cilghal, Mundi | error |
coder | Qwen 2.5 Coder 14B (LM Studio) | :1234 | all coding tasks | Council MLX → error |
Cloud tier runs through the Sanctum Proxy on :4040 with daily cost caps, audit logging, and automatic fallback to local models when the budget circuit breaker fires. The cloud proxy does not negotiate. It does math.
The Sanctum Proxy (port 4040) intercepts all requests and applies a 7-step pipeline before routing them to the appropriate model. Seven steps between an agent’s thought and the outside world. The TSA wishes they were this thorough.
- Smart content-based routing (model field, glob patterns, intent keywords)
- Anthropic prompt caching injection
- Thinking block sanitization
- Empty content block fixes
- Context window truncation
- Assistant message prefill stripping
- PII anonymization for OpenRouter
Config Example
Section titled “Config Example”services: lm_studio: enabled: true port: 1234 council_mlx: enabled: true port: 1337 voice_agent: enabled: true port: 1138 qwen3_tts: enabled: true port: 8008 proxy: enabled: true port: 4040Network Services
Section titled “Network Services”Bridges and tunnels. The unglamorous plumbing that connects a closet-mounted Mac Mini to a router, a mesh access point, a VM with no internet, and the wider world beyond the front door. If the core services are the organs, these are the nervous system — delicate, invisible when they work, and the first thing you suspect when something goes wrong.
There are nine of them. Two are SSH tunnels. Two are mDNS broadcasters. One talks to the router by first authenticating through a cloud server three thousand miles away. One talks to Sonos speakers because Docker couldn’t. Home networking in 2026 is the kind of helpful that gets people killed in horror movies.
| Service | Port | Codename | LaunchAgent | Description |
|---|---|---|---|---|
| SanctumBridge | 4078 | The FDA Neighbor | com.sanctum.bridge | Read-only HTTP proxy to FDA-protected SQLite databases (iMessage, WhatsApp, Contacts, Calendar). Jocasta-mcp queries through it so the MCP server itself doesn’t need Full Disk Access. |
| Firewalla Bridge | 1984 | Orwell — Big Brother watches | com.sanctum.firewalla | HTTP bridge to the Firewalla Purple router P2P API (port 8833). Bound to 0.0.0.0 so the VM can reach it. KeepAlive enabled. |
| Sonos Bridge | 1969 | — | com.openclaw.sonos-bridge | Native Mac SoCo REST API for 10 Sonos speakers. Replaces HA’s built-in Sonos integration. Handles TTS via XTTS, volume control, grouping, and announcements. KeepAlive enabled. |
| Orbi Bridge | 18080 / 18085 | — | com.sanctum.orbi-bridge | Socat bridge forwarding traffic from the VM to the Orbi access point (192.168.1.2 ports 80 and 5000). KeepAlive enabled. |
| Cloudflare Tunnel | — | — | com.sanctum.tunnel | Named tunnel sanctum-hub. Exposes health.example.net and ha.example.net via Cloudflare Zero Trust. KeepAlive enabled. |
| Network Control | 4007 | 007 — licensed to ping | com.sanctum.ha-tunnel | SSH tunnel forwarding port 4007 to the VM for Home Assistant integrations. |
| Health Ingester | 10101 | binary heartbeat | com.sanctum.health-tunnel | SSH tunnel forwarding port 10101 to the VM for the health data ingester. KeepAlive enabled. |
| mDNS Alias | — | com.sanctum.mdns-docs | Broadcasts haus aliases (sanctum-hub.local, holocron.local, etc.) via mDNS for LAN discovery. KeepAlive enabled. Consolidated from the old mdns-alias / mdns-dench split. |
Tunnel Routes
Section titled “Tunnel Routes”Two subdomains. Two Cloudflare Zero Trust routes. The entire external attack surface of the instance, right here in a table small enough to fit on a sticky note. That’s the goal. If your external exposure can’t fit on a sticky note, you have too much external exposure.
| Subdomain | Local Target | Purpose |
|---|---|---|
health.example.net | localhost:10101 | Health data ingestion endpoint |
ha.example.net | localhost:8123 | Home Assistant remote access |
Config Example
Section titled “Config Example”services: firewalla_bridge: enabled: true port: 1984 sonos_bridge: enabled: true port: 1969 orbi_bridge: enabled: true port: 18080 admin_port: 18085 cloudflare_tunnel: enabled: true tunnel_name: sanctum-hubSystem Services
Section titled “System Services”The immune system. The janitors. The 3 AM shift workers nobody thanks until something rots. These services watch the other services, rotate secrets before they expire, file documents nobody asked them to file, and occasionally reorganize your music library while you sleep. The system watches itself with more dedication than most humans watch their own cholesterol.
Eight background agents and three supporting services, zero ports for most of them, and one that requires you to physically plug in a hard drive like it’s 2008. We contain multitudes.
| Service | Port | LaunchAgent | Description |
|---|---|---|---|
| Watchdog | — | com.sanctum.watchdog | Runs every 600 seconds. Checks all enabled services and auto-heals failures via service-doctor. |
| Secret Rotation | — | com.sanctum.rotate-secrets | Runs on the 1st of each month at 3:30 AM. Rotates gateway tokens and updates Keychain entries. |
| iCloud Filer | — | com.sanctum.icloud-filer | Auto-filing daemon. Organizes documents from iCloud Drive into structured folders. KeepAlive enabled. |
| iCloud Backup | — | com.sanctum.icloud-backup | Periodic backup of Sanctum configuration and data to iCloud Drive. |
| VM Autostart (QEMU headless) | — | com.sanctum.vm-autostart | Launches QEMU headless on login, starts the Ubuntu VM, restores the bridge100 interface IP, and re-establishes the VM-facing LM Studio bridge on 10.10.10.1:1234. |
| Music Cleanup | — | com.sanctum.music-cleanup | Runs every Sunday at 3:15 AM. Organizes the Apple Music library via apple-music-organize.sh. |
| Kiwix | 8888 | com.sanctum.kiwix-serve | Offline knowledge library. Serves cached reference content. Requires external T9 drive. KeepAlive enabled with 30-second throttle. |
| Outline | 3100 | Docker container | Self-hosted wiki and documentation service. Provides a collaborative knowledge base for haushold documentation. |
| Jocasta MCP | CLI | CLI and Stdio RPC | The unified offline data proxy. Provides the Jedi Council safe, offline read-access to 16 disparate components: Apple Notes, Calendars, Contacts, Unified Logs, Maps, multiple messaging apps, and local file parsing. |
| Force Flow | 4077 | com.sanctum.force-flow | Notification triage and curfew enforcement engine. Mothma’s dispatch layer — decides what deserves attention and what gets filed under “haus is fine, stop asking.” M*A*S*H 4077th energy: triages the critical from the cosmetic with gallows humor and a functioning still. |
| SanctumBridge | 4078 | com.sanctum.bridge | FDA-privileged HTTP proxy to iMessage, WhatsApp, Contacts, and Calendar SQLite databases. Jocasta-mcp routes reads through this so jocasta-mcp itself doesn’t need Full Disk Access granted. |
| LiveKit Server | 7880 | com.sanctum.livekit-server | Private voice server for Yoda. Bound to Tailscale IP (100.0.0.25) only — no LAN or WAN exposure. RTC TCP companion on 7881. |
Config Example
Section titled “Config Example”services: watchdog: enabled: true settle_delay: 15 auto_fix: true dedup_window: 1800 secret_rotation: enabled: true schedule: "0 3:30 1 * *" icloud_filer: enabled: true kiwix: enabled: true port: 8888VM Services
Section titled “VM Services”On the other side of bridge100, in a QEMU-emulated box with no internet access, lives an entirely separate operating system running its own init system with its own opinions about how services should start. A whole different world. Twelve gigabytes of RAM. Eight CPU cores. Five personalities. Zero contact with the outside world unless the Mac says so.
The VM is, in the most literal sense, a brain in a jar. An air-gapped brain in a jar that runs your haushold security agent. We thought about this. We thought about this a lot. The architecture diagram made it look intentional.
| Service | Port | Codename | Systemd Unit | Description |
|---|---|---|---|---|
| OpenClaw Gateway | 1977 | Star Wars — the year hope was born | openclaw-gateway.service (user) | VM agent gateway with 1.5 GB heap. Runs 6 agents: Yoda (grand master), Mon Mothma (operations), Qui-Gon (infrastructure), Windu (security), Cilghal (health), Ki-Adi-Mundi (finance). |
| Docker | — | docker.service | Container runtime for any VM-side containers. | |
| SSH | 22 | ssh.socket | Remote access. Key-only auth with PQ key exchange enabled. |
Agent Details
Section titled “Agent Details”Six agents. One gateway. 1.5 gigabytes of heap memory. This is either a well-orchestrated council or a timeshare dispute waiting to happen. So far, the council metaphor holds. We’ll let you know if Windu stages a coup.
| Agent | Role | Specialization |
|---|---|---|
| Yoda | Grand Master | Senior council lead. Orchestration, council routing, final synthesis of complex decisions. |
| Mon Mothma | Operations | Force Flow and Living Force orchestrator. Incident correlation, boot sequences, cross-domain alignment. |
| Qui-Gon | Infrastructure | System health, Docker stability, automated recovery, memory triage. |
| Windu | Security | Security audits, Firewalla and PF rules, perimeter monitoring, daily security briefings. |
| Cilghal | Health | Wellness monitoring via Apple Health, cognitive profile analysis, genome-informed scaffolding. |
| Ki-Adi-Mundi | Finance | Triptyq Capital deal flow, personal fiscal health, expense categorization. |
The gateway uses SOPS+age encryption for secrets. The sops-start.sh wrapper decrypts environment variables at startup and never writes plaintext to disk. Secrets exist in cleartext only in RAM, only while the process runs. Paranoid? Maybe. But Windu insisted, and you don’t argue with the security agent.
VM Gateway Management
Section titled “VM Gateway Management”# Restart the VM gateway
# Check status
# View logsDeveloper Tools
Section titled “Developer Tools”One tool. It searches markdown. That sounds trivial until you have 287 documents spread across four repositories and you’re trying to remember which file documents the port that the service you’re debugging is supposedly listening on. Then it sounds essential.
| Service | Port | LaunchAgent | Description |
|---|---|---|---|
| QMD | — | — | On-device hybrid markdown search (v2.0.1). Combines BM25, vector similarity, and LLM reranking across 4 collections (287 documents). Indexes openclaw, skills, sanctum, and sanctum-docs. Exposes three MCP tools for Claude Code integration: keyword search, semantic search, and deep hybrid search. Nightly index refresh via docs-gardener. Metal-accelerated on Apple Silicon. |
Service Lifecycle
Section titled “Service Lifecycle”Every service follows the same lifecycle through the configuration system. Three states: enabled, disabled, and that liminal space where you changed the YAML but forgot to regenerate the plists. We’ve all been there. The watchdog has opinions about it.
Set enabled: true in instance.yaml, run generate-plists.sh, then load the LaunchAgent:
launchctl load ~/Library/LaunchAgents/com.sanctum.service-name.plistSet enabled: false in instance.yaml, unload the LaunchAgent, then regenerate plists:
launchctl unload ~/Library/LaunchAgents/com.sanctum.service-name.plist~/.sanctum/generate-plists.shThe watchdog checks enabled services every 10 minutes. A service is considered healthy if its port responds (for port-based services) or its process is running (for background agents).
# Manual health checksanctum_enabled openclaw_gateway && curl -sf http://localhost:1977/healthThree states, one truth: until generate-plists.sh runs and launchctl agrees, the YAML is just an opinion. The watchdog is the tie-breaker, and the watchdog has very little patience for opinions.
Port Summary
Section titled “Port Summary”Every Sanctum port — what it carries, where it lives, and the joke that justifies the number — lives at Port Summary, alongside the Deadpool Protocol that governs how new ports earn their numbers. Forty rows, forty cultural references, one architectural commitment that the infrastructure is going to be consistently absurd if it’s going to be absurd at all. Pulled out of this page so the service catalog can stay about services and the port catalog can be appreciated as its own art form.